Services
For Service call
+670 772 77677
+670 7857 0900
OUR SERVICES
Desktop Support
Managed Desktop Support Services from BSTT maximize the performance, security and reliability of your desktops while freeing your IT team to focus on strategic initiatives. We continually monitor your desktops, perform proactive maintenance, and manage security events and alarms. The service includes remote desktop support, an end-user support portal, and real-time and historical reporting on the health of your desktop environment.
Technology is great when it’s working, but a nightmare when it starts behaving strangely or doesn’t work at all. Our talented technical team has the experience, knowledge, and determination to identify the root cause and provide interim and long-term permanent solutions so that these problems stop reoccurring.We guarantee our solutions: if an issue reappears after we have reported it was fixed, we’ll fix it again for free until it’s properly fixed.
We help procure business class equipment for your business and ensure the devices are protected with warranties and follow the industry standardized hardware life cycles. By doing this we ensure your hardware is up to date with the latest firmware, replacement parts are available and there is no cost or fees to replace them, and we can proactively ensure you or your staff’s computer doesn’t fail while working on that executive report or client schematic.
Purchasing software has become a lot more complicated recently. Most software vendors have moved to subscription-based software; This sounds simple but it can get complicated with subscription addons and multi-user or multi-node licensing, or even processor licensing. Needless to say, you need someone familiar with software licensing to make sense of it all. Don’t pull your hair out, just ask us, and let our team handle it.
We offer virtual helpdesk services so that you and your staff can contact us for any IT issues. We log every email, phone call, or text so that we never miss or forget your issue. Our team can resolve issues via remote sessions or in person during an office visit.


CCTV and Surveillance systems
We specialize in providing CCTV systems for a variety of property types such as retail premises, education establishments, industrial sites and offices.
CCTV can be used to real time observation of images is required, a system may be designed to prompt the operator by configuring pre-set views, pre-determined camera sequences or providing triggers from events such as alarms or motion detection.

Social Media Marketing
Social media marketing refers to the process of gaining traffic or attention through social media sites. Social media itself is a catch-all term for sites that may provide radically different social actions. For instance, Twitter is a social site designed to let people share short messages or “updates” with others. Facebook, in contrast is a full-blown social networking site that allows for sharing updates, photos, joining events and a variety of other activities.

Server and Network Support
We take tech solutions seriously. That’s why we take the time to design and plan before purchasing or implementing a solution. We make sure you understand how a tech solution can make your life easier,and provide a cost analysis to help you make your decision. We also provide the essential documentation that describes the architecture, setup, and configuration settings, as well as the maintenance plan for supporting the solution after it’s been installed.

Networking and Cabling
We are is a full-service network infrastructure communications contractor in the field of structured cabling. Whether your requirements are voice, data, video, or fiber optic, our staff of well-trained professionals is here to ensure a quality installation.

Website and Apps Development
There is a lot that goes in to developing a website. Our development team works with you to ensure you love your websites layout, the graphics, and the overall feel that you want your visitors to experience
We help you get YOUR STORY out to your visitors
We want your business story to be reflected on your website. From your homepage to your contact page, all webpages will be professionally arranged to capture and hold the attention of your visitors, elevating your chances of lead conversions
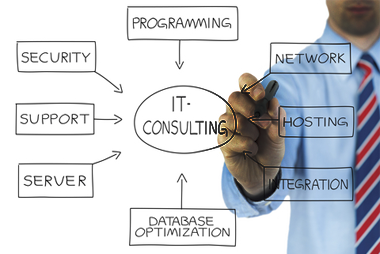
IT and Digital Consultant
IT consultants help individuals or businesses make technology purchases or strategy decisions and resolve technology challenges. An IT consultant may serve as a short-term virtual CIO, providing expert advice on IT strategy to a company that lacks high-level IT expertise in house.
We also does Creative and Content Management
To overcome this hurdle, companies need to look past traditional content marketing strategies and come up with a more creative and innovative approach. Creative content management has, therefore, emerged as the new face of content marketing.
